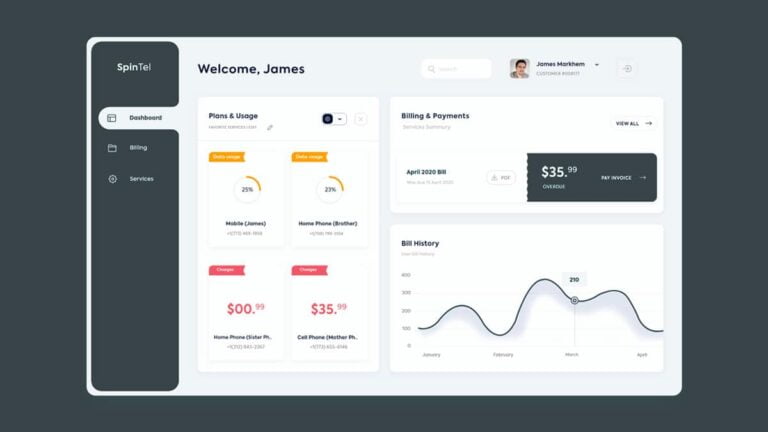
Identity and Access Management (IAM) has developed into a crucial component of many organizations’ security policies. Companies must make sure that their IAM tools and processes are configured properly in order to gain the most security advantages.
You can determine who has access to sensitive information and under what circumstances by enforcing best practices for identity and access management. To keep track of all of your components for present and potential dangers, you will need a thorough understanding of your company’s IT infrastructure. Here are some of the top trends in identity and access management that will help you get the most out of your cybersecurity program.
But first, let’s get one thing clear:
What Is Identity and Access Management (IAM)?
IAM, or identity and access management, is a framework of corporate procedures, rules, and technological advancements that makes it easier to manage digital or electronic identities. Information technology (IT) administrators can restrict user access to sensitive data within their businesses by putting an IAM architecture in place.
The identity and access management sector is always changing and improving. In fact, the Identity and Access Management (IAM) market was worth over $10 billion in 2018 and is predicted to expand at a CAGR of more than 10% from 2019 to 2025. However, there are certain core IAM best practices that can help your business as it develops its IAM strategy. You can expand your IAM architecture and fortify your security posture by using these best practices.
Adopting a Zero Trust Security Approach
Identity security is the cornerstone of a successful Zero Trust approach, and Zero Trust is a network security approach that is becoming increasingly important for every company. According to the Zero Trust approach, no user or program, inside or outside of an organization’s network, should be automatically trusted until their identity has been completely validated. This is also known as the “never trust, always verify” philosophy.
The least privilege concept, which ensures that all users have the least amount of access necessary to perform their jobs properly is another foundational component of a successful identity-centric Zero Trust architecture. Organizations must completely adopt the Zero Trust mentality in order to better safeguard crucial systems and data, especially as more and more employees work wholly outside of a corporate network and use many devices to get the work done.
Applying a Secure Password Policy
It is definitely not one of the Identity and Access Management (IAM) best practices to use weak passwords that are vulnerable to brute force attacks or credential stuffing. Strong passwords are always a solid foundation on which to build an effective IAM system. Passwords should be simple to remember and challenging to decipher or guess.
Setting up a password expiry policy is a smart idea. That way, employees will need to change their passwords frequently, and there won’t be any overdue passwords that are easy for hackers to crack. You can also make use of a secure password manager to make sure user passwords are stored safely and your employees don’t have to remember the passwords they create for each app or program.
Using Multi-Factor Authentication
Multi-factor authentication (MFA), which offers improved security and usability, is now one of the most effective security methods available. Upgrade to MFA if you’re still only using passwords for security. Relying on passwords can be bad practice to protect your company data as employees don’t always create secure passwords or update their passwords as frequently as they should.
The access request page and the place where the data is stored are separated by additional security measures added by multi-factor authentication systems. That additional layer can be a text message sent to the user’s phone or other security tokens. The more layers you have, the less likely it is that a breach will happen since the hacker will move on to the next prospective target. Cybercriminals are more inclined to take the path of least resistance.
Adopting Least Privilege
The use of the concept of least privilege is one of the most popular identity and access management best practices. IAM least privilege urges enterprises to impose as many restrictions on access and permissions as they can without impeding users’ normal work processes.
To be able to do this effectively, we specify the minimal set of rights that each role’s users must have in order to function. The objective is also to constantly evaluate the use and, whenever doable, decrease unused standing permits.
You can follow the typical security recommendation of allowing the least power or only the permissions necessary to complete a job when creating IAM policies. You should create regulations that only let users and roles carry out certain duties after determining what they must accomplish.
Regularly Checking Resource Access
The practice of regularly checking user behavior and resource access has various advantages. Understanding which resources are used can be done with the use of monitoring. Moving licenses from users who don’t utilize them to those who do can save operating costs. Enforcing least privilege access control measures in the context of cloud security might benefit from knowing which access rights are really used.
A person doesn’t require access to a resource if they aren’t using it. You should always keep track of the resources necessary for certain users to get their job done so that no user has access to resources they shouldn’t have.
To Sum Up
Network identities that are not adequately protected and maintained pose a real risk. A security team should never improperly or insufficiently handle these assets. The most important assets of your company shouldn’t be the easy target for the next incident or breach, whether it’s accounts that are lost or unidentified.
Identity and access management is always changing and evolving. The organizations that keep up with IAM developments in the future will remain competitive. IAM adoption rates are high as we go forward in the digital era. Organizational success depends on having a strong IAM suite with a clear future plan.